As organizations increasingly rely on technology to store and process sensitive information, the importance of cybersecurity cannot be overstated. Many organisations implement security risk management and compliance strategies to protect against potential threats and maintain a secure environment.
While these two approaches may seem similar, they are distinct concepts with different purposes and processes. Understanding the difference between security risk management and security compliance is crucial for organizations looking to safeguard their assets and data effectively.
This article will explore the key differences between security risk management and security compliance and how understanding these differences can help organizations improve their security posture.
Security Risk Management — Defined
Security risk management is identifying and mitigating potential threats to an organization. It involves the continuous assessment and evaluation of risks and implementing measures to prevent or mitigate them.
Purpose
The primary purpose of security risk management is to identify and mitigate potential organisational threats. This involves continuously assessing the organization’s vulnerabilities and implementing measures to reduce the likelihood and impact of potential security breaches. This could include implementing strong passwords, securing network infrastructure, and training employees on cybersecurity best practices.
The goal of security risk management is to protect the organization from harm. This includes physical harms, such as damage to facilities or equipment, and financial harm, such as the loss of sensitive data or the cost of recovering from a security breach.
Security Compliance — Defined
Security compliance, on the other hand, refers to the adherence to laws, regulations, and industry standards related to cybersecurity. It involves meeting specific requirements set by external bodies, such as government agencies or industry associations. Security compliance aims to avoid legal penalties and fines that can result from non-compliance.
Purpose
The main purpose of security compliance is to adhere to cybersecurity laws, regulations, and industry standards. This could include things like the Payment Card Industry Data Security Standard (PCI DSS) for organizations that handle credit card transactions or the Health Insurance Portability and Accountability Act (HIPAA) for healthcare organizations.
Meeting these requirements helps organizations avoid legal penalties and fines that can result from non-compliance. It also demonstrates to customers and other stakeholders that the organization is taking the necessary steps to protect sensitive information and maintain a secure environment.
Key Differences: Security Risk Management & Compliance
Despite serving similar purposes, security risk management and compliance have several key differences. One of the main differences is the focus of each approach. Security risk management is proactive, focusing on identifying and mitigating potential threats before they occur. Conversely, compliance is reactive, focusing on meeting specific requirements set by external bodies.
Another key difference is the process involved in each approach. Security risk management involves conducting a risk assessment to identify potential vulnerabilities and then implementing a risk management plan to address those vulnerabilities.
Compliance, on the other hand, is concerned with meeting specific requirements set by external bodies. This could involve implementing specific controls or procedures or providing documentation to demonstrate compliance.
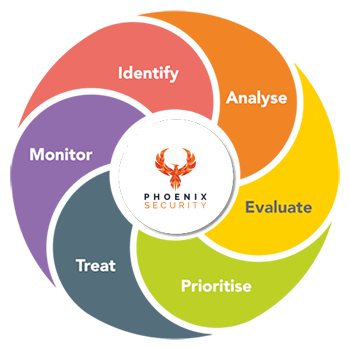
The Phoenix Security platform is a great tool for security risk management because it helps organizations analyze and contextualize potential threats across their attack surfaces. By taking data from security scanners and contextualizing, correlating, and prioritizing it, the platform offers a clear understanding of the actions that need to be taken to mitigate potential risks.
One of the key benefits of the Phoenix Security platform is that it provides a comprehensive view of an organization’s security posture. By analyzing data from multiple sources, it is able to identify potential vulnerabilities and prioritize them based on their likelihood and impact.
Phoenix Security — A Complete Security Risk Management Solution
Phoenix Security is a platform for security risk management because it helps organizations analyze and contextualize potential threats across their attack surfaces. By taking data from security scanners and contextualizing, correlating, and prioritizing it, the platform offers a clear understanding of the actions that need to be taken to mitigate potential risks.
One of the key benefits of the Phoenix Security platform is that it provides a comprehensive view of an organization’s security posture. By analyzing data from multiple sources, it is able to identify potential vulnerabilities and prioritize them based on their likelihood and impact.
Another advantage of the Phoenix Security platform is its ability to contextualize threats. By understanding the context in which a threat occurs, organizations are better able to understand the motivations behind an attack and the potential consequences of a breach.
Bottom Line
Both security risk management and compliance are important for the overall security of an organization. Security risk management helps identify and mitigate potential threats, while compliance ensures that an organization is adhering to relevant laws, regulations, and industry standards.
It is important for organizations to understand the differences between the two and implement both to protect against potential threats and maintain a secure environment effectively.













